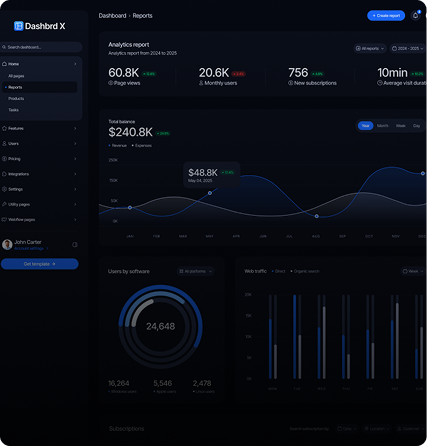
Get 24/7 visibility, proactive threat detection, and customized dashboards without the overhead of in-house IT teams or expensive enterprise tools.
Trusted by organizations that can’t afford downtime or data breaches.




Monitor networks, servers, applications, firewalls, cloud workloads, and databases with continuous real-time insights.
Detect threats early using behavioral analytics, log correlation, vulnerability detection, and threat hunting.
No expensive hardware. No learning curve. No extra staffing. Just results
Whether you manage 10 devices or 10,000, BestTechIT provides full-stack visibility and protection


HIPAA-ready monitoring & SIEM
PCI compliance, audit trails
OT network visibility
Cloud-native performance & security
Secure, compliant infrastructure
Our Virtual CISO service helps you manage risk, compliance, audits, and governance with certified security professionals who act as an extension of your team.
Schools and universities are no longer just places of learning — they are prime targets for cybercrime.
The BEST Friends of Education Program was created to safeguard students, faculty, and institutions from ransomware, data breaches, and operational shutdowns — without draining already-strained education budgets.
At BEST Consulting (BestTechIT), we stand with law enforcement agencies by supporting modern public safety and security operations with tailored technology solutions. Our expertise in network monitoring, system security, and real-time application tracking helps agencies respond faster, coordinate better, and protect communities with confidence.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Integer nec odio. Praesent libero. Sed cursus ante dapibus diam. Sed nisi. Nulla quis sem at nibh elementum imperdiet. Duis sagittis ipsum.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
At BEST Consulting (BestTechIT), we stand with law enforcement agencies by supporting modern public safety and security operations with tailored technology solutions. Our expertise in network monitoring, system security, and real-time application tracking helps agencies respond faster, coordinate better, and protect communities with confidence.
BEST Consulting believes in building smarter, safer, and more connected learning environments through technology. From secure network monitoring to application support for educational software, we help schools and institutions maintain reliable IT infrastructure so teachers can focus on teaching and students can focus on learning uninterrupted.
Phone: (863) 336-6880
Email: [email protected]
210 N. Missouri Ave #25123
Lakeland, Florida 33815

© B.E.S.T. Consulting. All rights reserved.